Connect Administration
Logging in to Connect
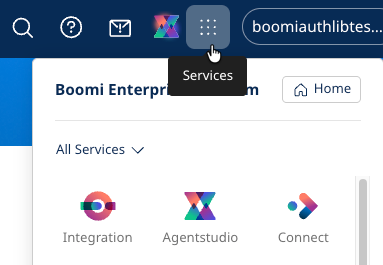
To access Connect, you need administrative privileges (ACCOUNT_ADMIN) on your Boomi account. Click on the Services menu, then select Connect.
The Connect home page is displayed, where you can perform the following actions:
- Creating configurations
- Editing configurations
- Creating identity providers
Creating configurations
To create a new configuration:
-
On the Connect Home tab, select Create Config and choose the connector you want to create a configuration for. You can search for a connector or scroll through the alphabetical list.
-
In the Create Config screen, enter the required information. Each connector has a different set of information needed. The following is a selection of some of the fields you may encounter:
- Config Name
- Identity Provider - Select an identity provider that has been defined for your organization.
- Account Identifier
- Account Name
- App ID
- Host Name
- Tenant Domain
- Authentication Management
- Access Token
- API Key
- Username & Password
- OAuth Client ID, Client Secret, and Scopes
-
The configuration is enabled by default. If you wish to disable it for any reason, you can toggle the Enabled switch.
-
In the Manage Tools section, you see a list of tools defined for this connector. By default, all of them will be enabled. You can disable any tool by toggling the Enabled switch.
-
Click Save to create the configuration.
-
A confirmation page appears with the following information:
- MCP URL - This is the URL of the MCP server that is registered with the MCP Registry
- Client ID
- Client Secret - Store the client secret safely since it will not be visible when you return to the configuration to view its details.
You will need this information when publishing the MCP server to your AI assistant.
- Click Done to create the configuration.
- (Optional) You can also create additional configurations for this connector by repeating the previous steps. You may want to use a different tenant or hostname, or a different set of enabled tools for a different user group, as defined by a different Identity Provider (IDP) role.
Editing configurations
To edit an existing configuration:
- Select the Configs tab on the Connect administration page. A list of all the configurations is displayed.
- Click the configuration name you want to edit.
- You can edit the name or the identity provider by clicking the Edit icon and then saving your changes.
- You can turn the configuration on or off by toggling the Enabled switch.
- You can enable or disable tools by clicking the Tools tab. Then, select the tools and click the Enable or Disable icon.
Creating identity providers
Setting up identity providers for your organization is an important step to automatically map user and AI tool access to enterprise permissions. Some sample identity providers include Okta, Microsoft Entra ID, Auth0, Ping Identity, Google Workspace, and ODIC. Be sure that you define the correct callback URI in your identity provider app. For example, if you want to use the US platform instance, you should set your callback URI to https://us.bc.boomi.com/oauth/identityprovider/oauth/callback.
Users will still need the proper credentials and permissions to perform an action. The Large Language Model (LLM) will respond if they do not have access due to their role. Some connectors also allow API keys to be entered for service-level users to grant higher authority.
If you have not created an identity provider, you will be prompted to create an IDP.
To create an identity provider:
- Select the Identity Providers tab on the Connect administration page. The Add Identity Provider page is displayed.
- Enter the following required fields to define your identity provider.
- Name
- Allowed Audience - The audience value expected in incoming tokens from this provider.
- Well-Known URL - The OpenID Connect discovery document URL for this provider.
- Client ID
- Client Secret
- Click Add Provider to save your new identity provider.
- (Optional) If you want to target different user groups with distinct permissions, you may want to create additional IDP roles to gain more granular control.
Refer to Microsoft Entra ID setup for detailed instructions.
